We share photos all the time, with friends, family, coworkers, or on social media. But every photo you take with your phone or digital camera contains hidden information called EXIF data that can quietly reveal a lot more than just the image itself — such as where and when you took the photo, what device you used, and what software you used to edit it.
That might seem harmless, but in the wrong hands, this invisible metadata can be used to track your location, piece together your daily routines, or dox you or your loved ones — exposing your identity, home address, or other personal data without your consent.
However, you can remove EXIF data to control how much information your photos reveal.
What is EXIF data and what is its purpose?
EXIF data (short for Exchangeable Image File Format) is hidden information automatically embedded in a photo when it’s taken with a digital camera or smartphone. It usually includes:
- Date and time the photo was taken
- Camera model and settings, like shutter speed, aperture, and ISO
- GPS location if location services are enabled
- Orientation (which way the camera was held)
- Editing software used, if any
Photographers can use EXIF data to filter images by identifiers such as camera model, focal length, ISO, or aperture settings. For example, they can examine past shots to understand why a photo turned out well (or didn’t) and adjust settings accordingly.
Image editing software can use EXIF information to automatically group photos by date or location, identify duplicates, or similar shots, suggest lens or exposure corrections, and allow you to search by metadata (for example, “photos in Paris”). It’s helpful for sorting vacation images or documenting events over time.
Why EXIF data can put your privacy at risk
EXIF data is invisible but rich in sensitive information. And if you share photos without removing it first, you could be putting your privacy — and that of your family, friends, coworkers, and clients — at risk.
Your photos might share your location
If GPS tagging is enabled, your images will include coordinates of where they were taken, potentially revealing:
- Your home address, workplace, or regular commute
- Private venues such as schools, medical facilities, or event locations
- Details about your vacation itinerary or business travel
- Client sites or restricted areas
For example, if you take a photo of your child at home, school, or a favorite playground and share it in a private group chat, there’s always a risk that someone could forward it, download it, or save it to a platform that scans location tags to learn more about what or who is in the image.
Time and date stamps can give away your routine
EXIF data also stores the exact date and time a photo was taken. When cross-referenced with other content — like social media posts or chat messages — it can:
- Reveal your daily habits or availability
- Pinpoint your location at a specific time
- Reveal patterns that could be exploited by stalkers or scammers
For instance, someone could check the timestamp of a photo you posted and match it with a public event or another person’s social media post — revealing who you were with and where you were.
Your device info says more than you think
Photos may include details like:
- The make and model of your phone or camera
- Editing software and version used
- Serial numbers (in some cases)
While not always sensitive, this data can reveal your professional tools, hint at your budget or expertise, or even help identify photos from a specific person or organization.
What happens when you upload to Google Photos
When you store your photos on platforms like Google Photos, you’re granting the company free access to the full EXIF metadata embedded in each one, including location, time, and device details.
Even if Google says it doesn’t use Google Photos content for ad targeting, it can and does scan every photo that’s uploaded and reserves the right to use your data to personalize services, improve its products, and build detailed user profiles. Just because Google doesn’t use your data for ads doesn’t mean it doesn’t collect it and use it elsewhere — or share it with other third parties.
If you’re concerned about this kind of tracking, consider turning off Google Photos backups.
AI makes it easier to track you through photos
Large language models (LLMs) make it easier than ever to extract and use the hidden details in your photos’ EXIF data. If someone gets access to a batch of your photos, they can feed them into an LLM to quickly pull out the metadata, organize it into neat tables, and make it easy to search and filter.
All these small details can be stitched together
On their own, each individual bit of information stored in EXIF data might not seem significant. But when combined and cross-referenced with the photo itself and other information — like your social media profiles — they can start to paint a much bigger and more personal picture.
Bad actors, advertisers, and data brokers can exploit this metadata to:
- Infer personal or professional details
- Track you or your team across platforms
- Build detailed behavioral or location profiles without your consent
How to see your EXIF data
You can easily see what kind of EXIF data your own photos are carrying without any special tools or skills. Remember, if you can easily access this information, so can anyone who has your photos.
On Windows, right-click the image file, select Properties, then go to the Details tab.
On Mac, secondary-click the image and select Get Info.
On iPhone or iPad, open the Photos app and swipe up on any photo.
On Android, open Google Photos and swipe up on a photo.
How to protect your privacy before sharing photos
Here are some tips to help you keep more control over what your photos reveal without changing how you take or share them.
Turn off location tagging on your camera
Disable location services in your phone’s camera settings so GPS coordinates aren’t saved with each photo.
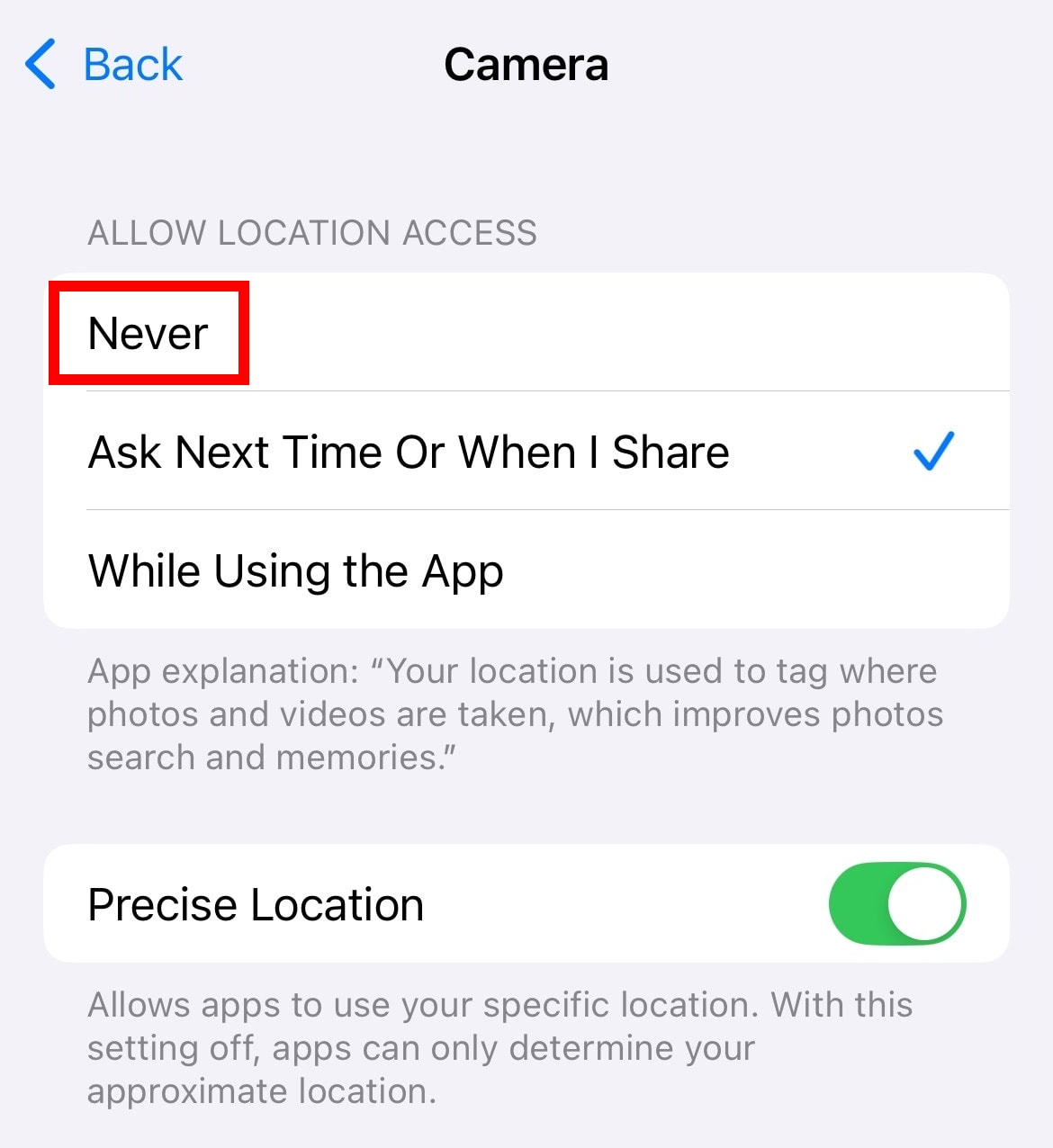
On iPhone, go to Settings → Privacy & Security → Location Services → Camera and tap Never.
On Android, open the Camera app, go to Settings, and toggle off Location tag.
Remove EXIF data before uploading or sharing
Always delete metadata before uploading your photos to websites, cloud storage, or messaging apps.
On Windows, right-click a photo, go to Properties → Details, click Remove Properties and Personal Information, and then select Create a copy with all possible properties removed.
Mac, iOS, and Android don’t have a built-in EXIF data remover, so you must use dedicated, third-party apps — such as ExifTool for Mac, Scrambled Exif for Android, and ViewExif for iOS.
Check and change file names
Even after removing EXIF data, the file name itself can still reveal information about a photo. For instance, Android includes the exact date and time the photo was taken in the file name — such as IMG_20250723_103045.jpg, which corresponds to July 23, 2025, 10:30:45 AM. WhatsApp makes things clearer by using file names like WhatsApp Image 2025-07-22 at 12.38.36 AM.
When sharing sensitive or personal photos, rename the files before sending or uploading them using neutral, non-descriptive names like photo1.jpg or image_001.png.
Check what’s visible in the photos
Beyond faces, your photos may contain subtle visual clues that can be used to identify people, places, or events:
- Street signs, license plates, or recognizable landmarks can reveal locations.
- Tattoos, jewelry, distinctive clothing, or reflections in mirrors and windows can expose identities.
- Background elements like screens, documents, schedules, or ID badges may contain sensitive information.
- Wall clocks, calendar dates, or smartwatch displays can pinpoint when a photo was taken.
Take time to review the entire frame before you share any image. Cropping, blurring, or redacting parts of the photo can go a long way in protecting privacy and safeguarding the people depicted.
And if you want to keep images from being reused or reposted without permission, you can also apply a repeating text or logo watermark using a watermarking tool. It’s not a replacement for blurring or editing, but it adds a visible layer of protection that makes misuse and AI scraping harder.
Remove EXIF data when sending emails
When sending sensitive images via email, Proton Mail helps protect your privacy by offering to remove metadata from attached photos before you send them. Here’s how to use this feature:
- Open Proton Mail, sign in, and click New message.
- Click the paperclip icon to attach your photo.
- When prompted, select Remove metadata, then choose whether to insert the image inline or as an attachment.
- Add your subject, write your message, choose the recipient, and hit Send.
Use private cloud storage that respects your privacy
Our cloud storage protects your privacy by design. Unlike other services, we can’t see your photos, their metadata, or any other personal information, thanks to a security model built on end-to-end encryption. Your files are encrypted on your device, stay encrypted during transfer, and remain encrypted while stored in the cloud. This means no one can see your photos except for you and the people you choose to share them with.
That said, Proton Drive doesn’t automatically remove EXIF data from your images. So if you’re sharing a photo that might say more than you’d like, it’s a good idea to manually remove the metadata first. Or, if you’re sending via email, you can use Proton Mail’s metadata remover for image attachments.